Client Support: (866) 437-6325
Sales Inquiries: (855) 788-4805
Secure IT Support
Strategic IT Support Throughout the Midwest
Dependable Solutions strengthens client operations with reliable, comprehensive outsourced IT support in La Crosse and throughout the Midwest.

OUR EXPERT TEAM KEEPS YOU SECURE AND COMPLIANT
Why Businesses Choose Dependable Solutions for IT Support in La Crosse
Proven Expertise in IT
With deep expertise, we deliver IT Support in La Crosse, prioritizing proactive management and performance optimization.
Dedicated Customer Service
We value our clients above all, providing consistent IT support that addresses unique challenges and aligns with your goals.
Swift Issue Resolution
Our responsive team minimizes disruptions, addressing problems at the source to ensure smooth, efficient operations.
Comprehensive Cybersecurity Protection
We defend your business with advanced cybersecurity, proactive monitoring, and regular assessments that safeguard your network, helping you focus on what matters most.
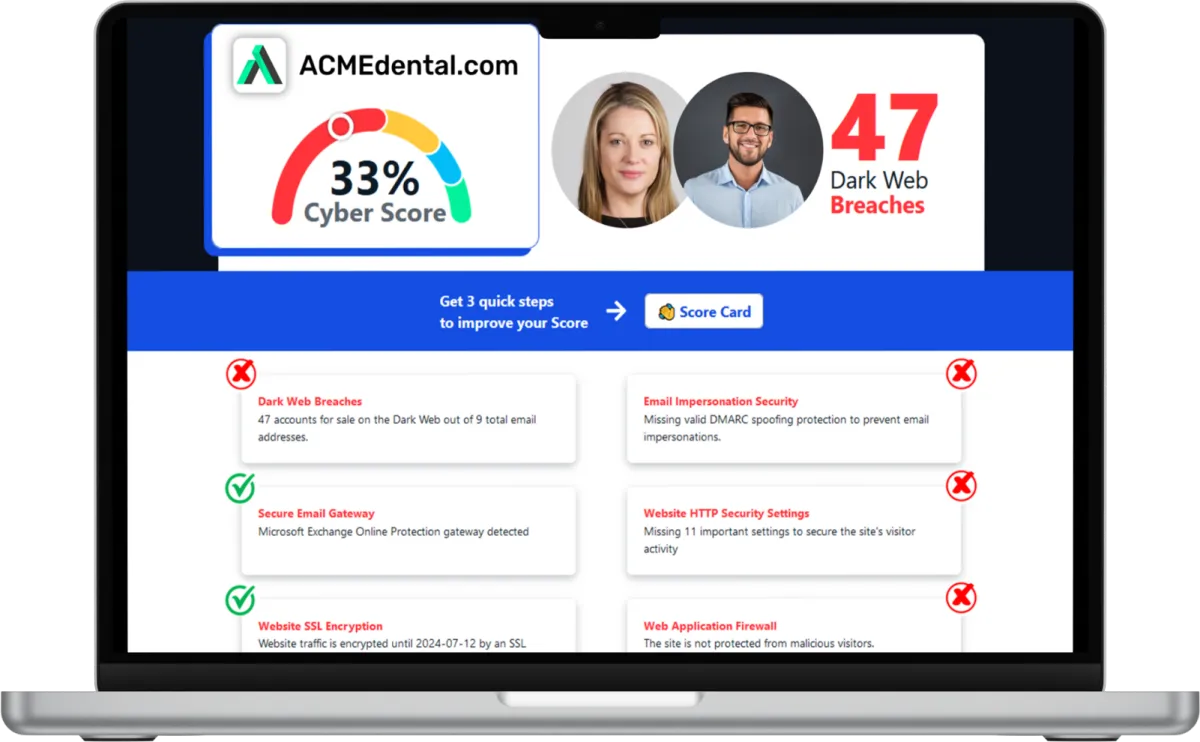
Want to see your Cyber Score?
Get it in 30 seconds!
Struggling with IT Roadblocks that Slow Your La Crosse Business Down?

Joe Ruskey
CEO, Dependable Solutions
Dependable Solutions is Here to Help.
When technology issues repeatedly disrupt your workflow, productivity suffers, and resources are drained. Dependable Solutions can help you overcome these challenges with proactive, customized IT support in La Crosse.
Are frequent technical problems impacting your business’s success?
With IT support in La Crosse, Dependable Solutions tackles your technology needs, addressing critical pain points and improving your daily operations. Our team provides efficient, security-focused support, so you can concentrate on driving your business forward without IT setbacks. Reach out today for reliable, comprehensive IT solutions to protect and streamline your business.
Call (855) 788-4805 today to schedule your appointment. We’re ready to start important IT conversations with businesses just like yours.
How Can We Help?
What We Do
Cybersecurity
We deploy layered defenses across endpoints, email, networks, and user behavior to protect your business, with continuous monitoring, rapid response, and security best practices.
End User Support
Our technicians resolve more than 85 percent of issues on first contact to keep your team productive, ensuring faster resolutions, happier employees, reduced downtime, and consistent quality.
Managed Networks
We design, install, and monitor your network infrastructure to ensure reliable connectivity and performance, with proactive monitoring, planning, and scalable architecture for growth.
Technology Management
Unified management of phones, cameras, and all other technologies your business or franchise relies on for daily operations, through centralized control and proactive maintenance.
What Clients Say About Us
Industry Insights and IT Best Practices
Stay informed on IT strategies, security tips, and industry insights to help your business in La Crosse stay resilient, efficient, and secure.

What You Should Know If Your Business Is Targeted By Ransomware
It may not be news to you that business ransomware attacks are on the rise, but the numbers may leave you shocked.
In 2020 alone, there were close to 300 million ransomware attacks worldwide. The cost of ransom payments demanded by hackers are also increasing in tandem with the increase in attacks. According to a recent projection, the global annual cost of ransomware attacks will touch $20 billion by the end of 2021.
Offerings like ransomware-as-a-service have made it easier for criminals with little technical knowledge to become threat actors. These attackers are less predictable and seem to lack a code of ethics. For example, groups in the past had lists of organizations they wouldn’t attack, such as cancer treatment facilities. That’s often not the case anymore.
A ransomware attack can affect any organization, regardless of size or industry. However, small and mid-sized businesses are the most vulnerable since cybercriminals count on these businesses to lack the resources to battle cybercrime or the IT teams to frequently evaluate cybersecurity measures. Even though small and mid-sized businesses continue to be disproportionately affected by these nefarious attacks, reporting and notifications rarely make the news unless a huge corporation experiences a breach.
With ransomware expected to hit businesses every 11 seconds, always remember that it isn’t a question of IF but rather WHEN your business will face ransomware attacks. Keep in mind that with the right security solutions and measures in place, your business won’t have to experience a devastating breach. But first, there are a few things you should know if you experience a ransomware attack.
Before Reacting To A Ransomware Attack, Remember:
The FBI advises against paying a ransom because spending money does not guarantee the hackers will share the keys to decrypt your data. While the FBI is an American organization, they raise a good point for businesses across the globe.
It doesn’t make any sense to place your trust in cybercriminals who have already demonstrated that they aren’t afraid to break the law and take advantage of you for financial gain. However, many businesses find themselves in this situation because they don’t have sufficient security, backup or compliance measures, and are desperate to get their data back.
Keep in mind that another reason the FBI advises against giving in to ransomware demands is that you are encouraging criminals to conduct further attacks. If nobody ever paid ransom, it’s likely there wouldn’t be as many ransomware attacks. Criminals would have to find new ways to make money and would disregard ransomware as a viable venture.
In case you fall victim to a ransomware attack and have no option other than paying, “ransomware negotiators” are available for hire. In ransomware negotiations, the most crucial moment occurs long before the victim and hackers discuss the ransom. This is because by the time both sides start to discuss, hackers have already gained considerable control over the organization’s network by encrypting access to sensitive business data and other digital assets. The more data they encrypt, the greater the negotiating power they have.
So, even before you begin negotiations, you need to know how much data has been compromised and what negotiating methods have been employed in the past by the criminals. Professional ransomware negotiators can help at this stage. Although a ransomware negotiation rarely results in a ransom demand being totally withdrawn, it can significantly bring down the asking price.
Victims Of Business Ransomware Attacks Should Expect The Following:
The data will not be erased in a trustworthy manner. It will be sold, improperly handled or stored for future extortion attempts.
Multiple parties would have handled the exfiltrated data, making it insecure. Even if the hacker deletes a large portion of the data once the ransom is paid, other parties who had access to it may have made duplicates to make payment demands later.
Before a victim can respond to an extortion attempt, the data may get leaked either intentionally or inadvertently.
Even if the threat actor explicitly promises to release the encrypted data after payment, they may not keep their word.
Make Your Move Before It’s Too Late
You’re probably wondering what steps you can take right now to combat the menace of ransomware targeting vulnerable systems. Our best recommendation is layered security.
Since no security technology or measure is flawless or guaranteed, layered security assumes that attackers will infiltrate different layers of an organization’s defenses or have already done so. The goal of this approach is to provide multiple security measures so that if an attack gets past one security tool, there are others in place to help identify and stop the attack before your data is stolen.
If the idea of protecting your business is overwhelming, don’t worry. You don’t have to do it alone. Collaborate with an experienced partner like us to do the heavy lifting for you. Our cybersecurity expertise and knowledge will help you pave the way to a more secure future. To get started, contact us for a consultation.
Frequently Asked Questions
What are IT security services?
IT security services encompass measures and practices to protect your systems, networks, and data from potential threats. These services include, but are not limited to, network security, data encryption, access controls, vulnerability assessments, penetration testing, and incident response.
What are managed IT service providers?
Managed IT service providers offer outsourced IT management and support, handling a company's technology needs so the business can focus on core operations.
What are the benefits of cybersecurity services?
IT security services encompass measures and practices to protect your systems, networks, and data from potential threats. These services include but are not limited to network security, data encryption, access controls, vulnerability assessments, penetration testing, and incident response.
Experience Reliable IT Support in La Crosse with Dependable Solutions
Dependable Solutions is dedicated to providing trustworthy, secure IT Support that empower your business in La Crosse to operate smoothly and grow confidently. Partner with us for dependable, proactive support that aligns with your unique goals and challenges.
Call (855) 788-4805 today or click the button below to schedule your appointment. We’re ready to jumpstart your IT journey.
Subscribe to our newsletter
Subscribe to our newsletter for exclusive updates and insights delivered straight to your inbox!